From Legacy to Leading Edge: A visual journey through the evolution of security technology
 By Gina Stuelke, CEO of Kenton Brothers
By Gina Stuelke, CEO of Kenton Brothers
Back in 2008, our industry experienced a significant convergence event joining physical security and IP based networks onto a common platform. This was a major shift away from the disparate systems we had become accustomed to. That seems like such a long time ago! Today, we are involved in another convergence event involving physical security and cyber security.
The two pyramids in the images below represent the technology stacks used by Kenton Brothers, with each layer reflecting the progression of security technologies and how our offerings have elevated over time.
Kenton Brothers 2008 Technology Pyramid
 1. Base Layer (Mechanical Locking Hardware): Traditional, physical locking systems.
1. Base Layer (Mechanical Locking Hardware): Traditional, physical locking systems.
2. High Security Cylinders and Masterkey System Implementation: The introduction of advanced physical keys and locks.
3. Legacy and Stand-Alone Access Control and Analog Video Surveillance Systems: Initial electronic security measures, such as standalone access systems, video surveillance and analog technologies.
4. Network-Based (IP) Access Control and Video Surveillance Systems: The shift to internet-based systems, improving remote access and integration.
5. Integration Services: Combining different systems (video, access control, etc.) for better coordination and ease of use.
6. Hosted and Managed Services: Outsourcing and cloud-based security management to external providers.
7. Video Analytics: Using software to analyze video data and identify suspicious activities automatically.
Kenton Brothers 2024 Technology Pyramid
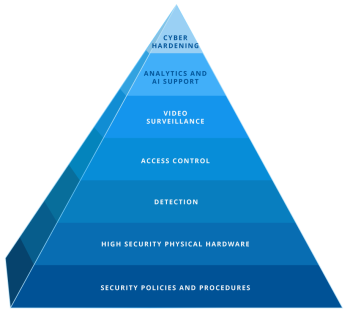 1. Base Layer (Security Policies and Procedures): Security begins with robust organizational policies and procedures, a foundational aspect in modern security systems.
1. Base Layer (Security Policies and Procedures): Security begins with robust organizational policies and procedures, a foundational aspect in modern security systems.
2. High Security Physical Hardware: Continues from previous physical security technologies but is more sophisticated.
3. Detection: Active detection systems for unauthorized access or incidents (includes sensors, alarms, etc.).
4. Access Control: Advances in access control technology (includes biometric and smart credentials).
5. Video Surveillance: Video monitoring remains central, but with higher resolution, better storage, and cloud integration.
6. Analytics and AI Support: Modern video surveillance includes AI, improving event detection and proactive analysis.
7. Cyber Hardening: Reflects the growing importance of cybersecurity, securing systems from hacking and digital threats.
What are the comparisons in technological advances?
- Shift from Analog to IP: Over the last decade, analog systems (present in the first pyramid) have largely been replaced by IP-based systems, which allow for higher quality video and easier integration into larger networks.
- Integration of AI and Analytics: Modern systems (second pyramid) emphasize the use of AI for proactive security management. This shift moves beyond video analytics to AI-supported threat detection, reducing human workload and improving accuracy.
- Focus on Cybersecurity: The first pyramid lacks any mention of cybersecurity, which has become essential in modern security infrastructures due to the increasing threat of hacking. Cyber hardening in the second pyramid highlights this critical evolution.
- Increased Use of Cloud Services: The second pyramid also reflects advances in cloud technologies for video storage, processing, and real-time analytics—leading to more flexible, scalable, and manageable systems.
- Detection Technologies: Detection is more advanced in the second pyramid, likely including smarter sensors and automated systems integrated with AI.
Security systems have evolved from primarily physical and standalone solutions (first pyramid) to highly integrated, AI-driven, and cyber-secure ecosystems (second pyramid). These technological shifts have led to more automated, efficient, and intelligent systems capable of responding to modern-day security threats.
Has your commercial security stack been in place for a long time? It may be time to take a good look to make sure you are keeping up with the aggressive changes in technology. And if you need help, please give us a call!




Leave a Reply
Want to join the discussion?Feel free to contribute!