Anti-Passback and Anti-Tailgating: Do you know who is in your building?
By Neal Bellamy, IT Director at Kenton Brothers
Do you know who is in your building? Do you know where everyone is located when they are in your building?
To help companies answer these questions, we use access control solutions. (As the name implies, these solutions control access to buildings.) When configuring these systems, we decide which people get into the building, which doors they can use and the times that they are able to open the door. Access cards are a key component of these systems.
Access Card Skimming Devices
 There are reasons why you might want to increase security or safety by adding more features to your current access control system. Why? Copying and emulating an access card has become easier, due to new technology like a flipper zero and other skimming devices.
There are reasons why you might want to increase security or safety by adding more features to your current access control system. Why? Copying and emulating an access card has become easier, due to new technology like a flipper zero and other skimming devices.
The best defense against copying a card is to use a card technology that has not yet been hacked. You also need to use encrypted communication between the reader and the control panel. (Both have been talked about before in my previous blogs). However, sometimes the upgrade path can take a long time to implement and/or be expensive depending on how large your system is and how old it is. Another way to guard against skimmers might be to ensure a card has only been used once to gain entry.
Anti-Passback
 Anti-passback is the access control term when we want to prevent someone from entering a door and then passing back the card to another person, who then uses the card to enter. Most access control systems have that technology available. When this feature is enabled, you also know when a person is leaving the area. If you know when they are in the area and you know when they leave an area, then you also know where they shouldn’t appear in the building. In other words, if the cardholder is already in the building, you should not grant access to the building again.
Anti-passback is the access control term when we want to prevent someone from entering a door and then passing back the card to another person, who then uses the card to enter. Most access control systems have that technology available. When this feature is enabled, you also know when a person is leaving the area. If you know when they are in the area and you know when they leave an area, then you also know where they shouldn’t appear in the building. In other words, if the cardholder is already in the building, you should not grant access to the building again.
The reason an employee might try to get into the building again is because they loaned their card out, or because it was copied. Anti-Passback also provides more safety. If an emergency happens, you also know who was in the building or area at the time of the event. If you don’t have Anti-Passback enabled, you might know that a person came in that morning, but would not know that they left for lunch or an appointment during a specific timeframe.
To build on this example, imagine a multi-building company or a company located across multiple cities. If someone badged into the downtown campus and has not badged out, then they can’t possibly be at the uptown office. If they were in the New York office at 8am, there is no way they could be badging into the L.A. office at 9am.
Anti-Tailgating
You can also define areas within areas. You might have a building perimeter, then a lab inside, and maybe even a hazardous storage area inside the lab. You can set the rules so that they cannot enter the storage area unless they are in the lab first; You can’t enter the lab until they are in the building; and so on. (This technically is called Anti-Tailgating, but goes hand-in-hand with Anti-Passback.)
There are a few reasons you might want to know in real-time who is in your building. Anti-Passback and Anti-Tailgating can improve security by only allowing one person to be in one place, improve safety by knowing that someone was in the building during an emergency, and even help you understand where in the building someone is located.
We are experts at solving hard problems, if you have a unique situation, please let us help.

 Redundancy servers are put in place to keep things up and running in the event of a hardware failure. The engineering definition of redundancy is, “the inclusion of extra components which are not strictly necessary to functioning, in case of failure in other components.”
Redundancy servers are put in place to keep things up and running in the event of a hardware failure. The engineering definition of redundancy is, “the inclusion of extra components which are not strictly necessary to functioning, in case of failure in other components.” Commercial video surveillance systems rarely have server redundancy. If a server fails, the cameras will no longer be recording. Some management systems have capabilities for server failover built into the software. Unlike with an access control redundancy server where you have the hot or cold option, a video redundancy is likely going to be a hot redundancy server. If the initial server goes down, the redundancy server starts recording the video streams. Obviously, the big win in this scenario is that you mitigate the risk of lost video when you have a hardware failure at the worst possible time (when a security event is happening).
Commercial video surveillance systems rarely have server redundancy. If a server fails, the cameras will no longer be recording. Some management systems have capabilities for server failover built into the software. Unlike with an access control redundancy server where you have the hot or cold option, a video redundancy is likely going to be a hot redundancy server. If the initial server goes down, the redundancy server starts recording the video streams. Obviously, the big win in this scenario is that you mitigate the risk of lost video when you have a hardware failure at the worst possible time (when a security event is happening). A “Cold” redundancy server is one that is set up and has the systems already installed, but is not running in parallel. While it is ready to be put into production if the main server fails, there is some setup that has to occur. At minimum, restoring services requires booting up the redundancy server. However, other requirements might include installing the latest backup of card holders, schedules, routing all devices to the new server, getting the IT team and daily operations team involved. While all of those things are happening, the primary server is down. No changes to the configuration can be applied across an access control system and no video streams are being recorded until the cold redundancy server is brought online.
A “Cold” redundancy server is one that is set up and has the systems already installed, but is not running in parallel. While it is ready to be put into production if the main server fails, there is some setup that has to occur. At minimum, restoring services requires booting up the redundancy server. However, other requirements might include installing the latest backup of card holders, schedules, routing all devices to the new server, getting the IT team and daily operations team involved. While all of those things are happening, the primary server is down. No changes to the configuration can be applied across an access control system and no video streams are being recorded until the cold redundancy server is brought online. By
By  Just like other door hardware, door closers also come in different grades and standards for the type of opening they are being installed into. For instance, an exterior opening that sees a lot of foot traffic during the day should have a Grade 1 closer whereas a closet internal to the building that may be used rarely may not need a Grade 1 closer. A Grade 2 closer would be sufficient in this instance.
Just like other door hardware, door closers also come in different grades and standards for the type of opening they are being installed into. For instance, an exterior opening that sees a lot of foot traffic during the day should have a Grade 1 closer whereas a closet internal to the building that may be used rarely may not need a Grade 1 closer. A Grade 2 closer would be sufficient in this instance.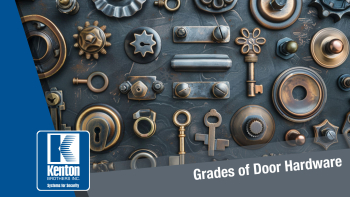 Commercial grade hardware is built to withstand areas with higher amounts of traffic than residential buildings require. Essentially what you put on your home isn’t the same as what goes on the front door of a highly used commercial space. Along with commercial hardware being heavier duty, most commercial buildings have specific requirements when it comes to meeting certain specifications such as UL Listings, ADA compliance, or other life safety conditions.
Commercial grade hardware is built to withstand areas with higher amounts of traffic than residential buildings require. Essentially what you put on your home isn’t the same as what goes on the front door of a highly used commercial space. Along with commercial hardware being heavier duty, most commercial buildings have specific requirements when it comes to meeting certain specifications such as UL Listings, ADA compliance, or other life safety conditions.

 In a distant medieval realm, nestled between rolling hills and dense forests, there existed a peaceful village named Eldoria. The villagers, content in their simple lives, lived in harmony with the land. However, peace is a fragile thing, and the tranquility of Eldoria was shattered when rumors of marauding bandits spread like wildfire. Travelling caravans spoke of their perils and the destruction left behind by these marauders.
In a distant medieval realm, nestled between rolling hills and dense forests, there existed a peaceful village named Eldoria. The villagers, content in their simple lives, lived in harmony with the land. However, peace is a fragile thing, and the tranquility of Eldoria was shattered when rumors of marauding bandits spread like wildfire. Travelling caravans spoke of their perils and the destruction left behind by these marauders.