CyPhy Part 3 – Breaking down CISO and CSO silos to reach Security Convergence.
By David Strickland, Vice President of Kenton Brothers
 The third of a three part series covering the Cybersecurity and Infrastructure Security Administrations (CISA) newest announcements around Security Convergence. Kenton Brothers Systems For Security hopes to help organizations understand this concept and adopt best practices for securing the Cyber-Physical Systems (CPS) currently deployed.
The third of a three part series covering the Cybersecurity and Infrastructure Security Administrations (CISA) newest announcements around Security Convergence. Kenton Brothers Systems For Security hopes to help organizations understand this concept and adopt best practices for securing the Cyber-Physical Systems (CPS) currently deployed.
(Part 1 | Part 2 | Part 3 | Part 4)
In part two, we discussed the size of the problem we have worldwide with the advent of 46 Billion IOT and IIOT devices. In this blog, we will concentrate on breaking down the CISO and CSO silos and the specific steps an organization can take to reach Security Convergence.
Breaking down the Walls
In a Siloed Organization…
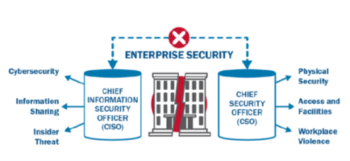 Security functions operate independently with limited collaboration on enterprise-wide risks. Senior leaders and teams lack the visibility of interconnected physical and cyber assets. Lines of communication are unclear and impede coordination and collaboration. Organizations are unable to quickly identify, prevent and respond to complex threats.
Security functions operate independently with limited collaboration on enterprise-wide risks. Senior leaders and teams lack the visibility of interconnected physical and cyber assets. Lines of communication are unclear and impede coordination and collaboration. Organizations are unable to quickly identify, prevent and respond to complex threats.
The Solution:
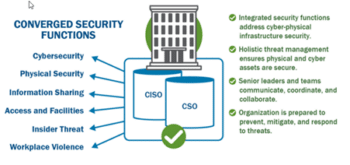
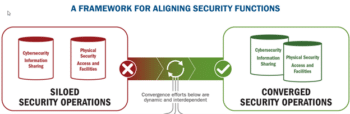
Organizations with converged cybersecurity and physical security functions are more resilient and better prepared to identify, prevent, mitigate, and respond to threats. Convergence also encourages information sharing and the development of unified security policies across security divisions. To accomplish a converged effort, you must first break down the walls that hold each siloed department back.
How does an organization do that? Through Communication, Coordination and Collaboration.
Communication, Coordination and Collaboration
COMMUNICATION
- Initiate a Dialogue
- Enable Communication with security leaders. Engage with upper management to discuss what convergence might look like. Successful convergence relies on support from leadership
- Review Leadership Roles
- Identify the leaders of this movement
- Establish a Convergence Team
- Convergence Team – Identify key players such as CSO or CISO, Physical Security personnel, IT personnel and facility managers
- Enable Information Sharing
- Engage with team members across all security functions to identify points of convergence
COORDINATON
- Formalize Convergence team roles and responsibilities
- Establish a cadence and structure for team coordination
- Identify Linked Assets
- Coordinate with team members across security functions to assess cyber and physical assets and which ones are linked. Assess the risk of each
- Conduct a Vulnerability Assessment
- Identify gaps in security and risk mitigation and determine where gaps may be closed through convergence
- Determine the Baseline
- Leverage the information gained in your assessments and gap analysis to determine your baseline for security operations and incident mitigation
COLLABORATION
- Run the Numbers
- Determine if convergence on any scale is financially feasible from short-term and long-term perspective
- Prioritize Improvements
- Identify and prioritize improvements, including patches, software updates, virus protections, certificate management, and opportunities for automation – There are some powerful options here
- Craft Risk Driven policies
- Develop and implement risk driven policies with broad reach that reflect converged security functions. Identify best practices. There are some powerful options here as well
- Strategic Alignment
- Align strategy to shared practices and goals. Focus on improving efficiency and increased information sharing
An integrated threat management strategy reflects in-depth understanding of the cascading impacts to interconnected cyber-physical infrastructure. As rapidly evolving technology increasingly links physical and cyber assets—spanning sectors from energy and transportation to agriculture and healthcare—the benefits of converged security functions outweigh the challenges of organizational change efforts and enable a flexible, sustainable strategy anchored by shared security practices and goals.
Kenton Brothers Systems for Security is ready to help your organization take on this task. We can help facilitate conversations or simply conduct assessments that can help springboard the effort. Give us a call today.
Resources
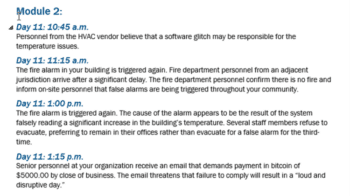
There are many resources available to get this conversation started. One of our favorites is the table top exercise templates provided by CISA. You can find them at www.CISA.gov. The table top exercise gives you real world scenarios and asks you to use it in your planning. These are a really comprehensive tool that will have immediate impact on your discussions.
This is one of the best articles I’ve read on the subject (outside our blogs)
Convergence questions answered – Control Engineering Europe
Again, thank you for joining us on this three-part series. We are standing by to help in any way.





Leave a Reply
Want to join the discussion?Feel free to contribute!