By Neal Bellamy, IT Director at Kenton Brothers
In the last couple of months, we’ve been designing our intrusion system, network infrastructure, and video surveillance systems. Now it’s time to design the access control system.
Access Control
There can be lots of advantages to Access Control.
Because the doors are controlled electronically, we can:
- Automate the open and close time of the business or areas
- Stop handing out keys that might not be turned back in or lost
- Track who goes where, etc.
- Use access control doors for business reasons, not just for security.
 First, let’s talk about the components of access control. A couple of the components are obvious, but others are misunderstood. Today we’ll talk about card readers, locks, door position sensors, request to exits, and credentials. Exciting, right? Maybe not, but these are incredibly important details for a commercial security system.
First, let’s talk about the components of access control. A couple of the components are obvious, but others are misunderstood. Today we’ll talk about card readers, locks, door position sensors, request to exits, and credentials. Exciting, right? Maybe not, but these are incredibly important details for a commercial security system.
Card Readers
Card readers are the most obvious component required in an access control system. The card reader is what reads your access control card and identifies you to the system. Your card is unique to you within your access control system. However, a card reader doesn’t have to be just a card reader.
There are lots of ways to identify yourself to the system. Fingerprint readers, vein readers, pin pads, iris scanners, and face scanners are all possible ways that you could be identified. Some of these are more secure than others. Pin numbers can be shared, so we highly suggest not using them, or make sure that whatever you have behind the door is not valuable.
Fingerprint readers are more hackable (YouTube Video about that here) than a vein, iris or face scanners. The highest level of security is two-factor authentication. You would use two of these kinds of credentials to enter the door at the cost of being less convenient.
Locks
 Locks are the next most obvious component. You need to be able to lock and unlock the door electronically. Common electronic locks are Electrified Panic, Electrified Levers, Strikes and Mag (magnetic) locks.
Locks are the next most obvious component. You need to be able to lock and unlock the door electronically. Common electronic locks are Electrified Panic, Electrified Levers, Strikes and Mag (magnetic) locks.
All electronic locks can be broken into two categories, “Fail-Safe” or “Fail-Secure”.
Fail-Safe locks unlock when there is no power going to them. When the power “Fails” the lock is “Safe”. In this case, “Safe” means someone can get out. Unfortunately, that also means that the door is unlocked, so someone could come in if the power fails.
Fail-Secure is the opposite; when the power fails, the lock is secure or locked. There are times when codes require a Fail-Safe lock, like in a stairwell of a large high rise, however, at Kenton Brothers we prefer fail secure locks.
Electrified Panic, Electrified Levers, Strikes can all be Fail-Secure or Fail-Safe, but mag locks are always Fail-Safe. Mag locks usually require two forms of egress, meaning that there are two ways to leave the building through a mag lock. Mag locks generally are also required to be connected to the fire alarm. Although Mag locks themselves can be cheaper than other types of locks, by the time you connect the two forms of egress and the fire alarm, you could have installed a Fail-Secure lock.
Door Position Switches
Now you can authenticate at the door with a reader and unlock the door with an electrified lock. But how do you know if someone propped open the door, or forgot to shut it? That’s where the third component at the door comes in, the door position switch.
This switch is generally a magnetic switch mounted in or on the door that tells the system if the door is open or closed. You can use this information to drive alerts if a door is left open too long, which circumvents the security that you are trying to establish with access control.
Wouldn’t it be nice to know if someone opened the door that was unauthorized? With the door position switch, we can tell the door opened without a card read, but it would also alert us when anyone leaves the building.
Request to Exit
We use a second type of switch to tell us when someone is leaving the building called a “Request to Exit”. This can be a motion detector that triggers when someone gets near it, or it can be built into a lever or exit bar. That way, if the doors opens, but the request to exit was not triggered and the reader was not used, we know someone came in from the outside and was not authorized. This is called a “Door Forced”. The door was forced open with key or crowbar.
Credential
The last component is a credential. We say credential, not card, because we can use a key fob, iris, face, fingerprint or other identifying feature to authenticate to the system. Most systems use a card or key fob, because of cost and ease of use. However, not all cards and key fobs are the same.
There are dozens of technologies that can be used to store and transmit the credential number to the system. Some are proprietary, some are open, some are not-encrypted and some are. Generally, we advise clients to use a “Smart Card” technology that is encrypted, but not proprietary. It provides the security of encryption while allowing the technology to be compatible with most access control systems. Some options even guarantee that your exact credential number will never be available to any other company in the world, while also being non-proprietary and encrypted.
So What Will Kenton Brothers Be Using?
Whew, that was a lot of info! Now let’s talk about the solution we’re going to use at Kenton Brothers.
Our exterior doors need to be secure, while some of our interior doors are really just for traffic control. We will control our space while also controlling the tenant space. There’s an overhead garage door leading from our space to a space shared with the tenants. We also have an overhead garage door for loading and unloading material that we don’t want to have to get out of the truck to open.
For the exterior doors, we’ll install an electrified exit bar with a built-in request to exit. The exit bars are heavy duty and allow a large number of people to get out of the building. The built-in request to exit also gives less false triggers than motion detectors, because instead of triggering when someone gets close, it only triggers when someone actively leaves the building by presses the bar down. These doors will also get a door position sensor.
The interior doors will be strikes or electrified levers. Although these locks are still rated as “Heavy Duty” they are a little less expensive and won’t see as much use. We will still use request to exits in the electrified levers, for the same reason as the exit bars. We’ll still use a door position sensor to make sure the doors are closed.
The overhead doors will be controlled by door operators, kind of like your garage doors at home. We’ll tie those into the access control system.
For the readers, we’ll use HID iclass SE. These are non-proprietary, encrypted readers, which can also be used with Bluetooth credentials. Right now, they will connect with the Weigand protocol, an open standard communication between readers and access control systems. They can also use a newer, more secure OSDP protocol when the access control systems are ready.
For the long range reader at the exterior overhead door, we’ll use a Nedap reader that can read a special credential at distances up to 33 feet away. That way, the door can be opened without leaving the comfort of the truck.
Thanks for joining me on this physical security journey for our new building. We are really excited to create a showpiece of security layers and technologies.
Please stop by this summer to see everything we’re integrating to create a holistic security stance!
 A large warehouse customer of ours was in a lot of pain when it came to their various security systems.
A large warehouse customer of ours was in a lot of pain when it came to their various security systems.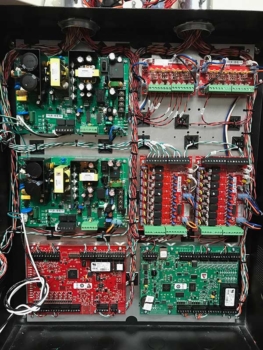 To ease their pain on Video Surveillance and Access Control, we brought in Avigilon.
To ease their pain on Video Surveillance and Access Control, we brought in Avigilon. The timeline for the installation was short, so we used several guys from the Kansas City office to get the job done.
The timeline for the installation was short, so we used several guys from the Kansas City office to get the job done.





 Most people are familiar with the phrase, “Do you eat your own cooking?” This is a casual way to ask a company if they implement the same products and services they’re selling their customers in their own business.
Most people are familiar with the phrase, “Do you eat your own cooking?” This is a casual way to ask a company if they implement the same products and services they’re selling their customers in their own business.
 Stacy Wessing and Brian Nutt from our Mid Mo team have worked with the City of Columbia for over 10 years on numerous projects, some of which included battery backup systems for their data centers, virtualization software, networking equipment, and downtown surveillance cameras. Brian and Stacy have also worked at a previous employer together with some of the City’s current staff. The City knew we could deliver on a project as promised from previous successful experiences and a solid relationship.
Stacy Wessing and Brian Nutt from our Mid Mo team have worked with the City of Columbia for over 10 years on numerous projects, some of which included battery backup systems for their data centers, virtualization software, networking equipment, and downtown surveillance cameras. Brian and Stacy have also worked at a previous employer together with some of the City’s current staff. The City knew we could deliver on a project as promised from previous successful experiences and a solid relationship.