By David Strickland, Vice President of Kenton Brothers
 At Kenton Brothers Systems for Security, we are always focused on Innovation. We have a great saying: Innovate or Die
At Kenton Brothers Systems for Security, we are always focused on Innovation. We have a great saying: Innovate or Die
The physical security industry is undergoing a major transformation as artificial intelligence (AI) becomes an integral part of surveillance, access control, and threat detection systems. AI-driven security solutions are enhancing the effectiveness of security personnel, improving response times, and reducing operational costs. As organizations seek more proactive approaches to risk mitigation, investments in AI technology continue to surge across various sectors, including corporate enterprises, critical infrastructure, law enforcement, and public safety.
According to market research, the global AI spend in the security market is expected to reach $71 billion by 2027, growing at a CAGR of over 23%. Major players in the industry are investing billions in AI-powered surveillance, access control, and cybersecurity solutions, recognizing the immense potential of these technologies to reshape security operations.
AI-Powered Video Surveillance
AI is revolutionizing video surveillance by improving object recognition, behavior analysis, and real-time anomaly detection. Companies like Hanwha Vision and Axis Communications are embedding deep learning algorithms into their cameras, allowing for advanced analytics such as facial recognition, license plate recognition, and suspicious activity detection.
Traditional security systems often rely on motion detection, which can trigger numerous false alarms due to environmental factors like shifting shadows, animals, or weather conditions. AI-powered analytics refine this process by differentiating between routine activities and actual security threats. By leveraging neural networks and machine learning, AI can accurately identify threats such as unauthorized intrusions, abandoned objects, or aggressive behavior. As a result, security teams can prioritize real incidents and respond more efficiently, minimizing downtime and improving security operations.
Additionally, AI-enhanced surveillance systems can integrate with law enforcement databases, allowing for real-time identification of persons of interest, missing individuals, or stolen vehicles. This level of automation significantly enhances the ability to act quickly in high-risk scenarios.
Predictive Threat Detection and Incident Prevention
One of the biggest advantages of AI in security is its predictive capabilities. AI algorithms analyze vast amounts of historical data to identify patterns and predict potential security breaches. By integrating AI with physical security measures, organizations can take preventive action before incidents occur, reducing risks and enhancing preparedness.
For example, AI-driven behavior analytics can detect unusual activity in high-security areas, such as loitering near restricted zones or unauthorized access attempts. Advanced AI models can factor in variables like time of day, frequency of movement, and crowd density to determine whether an individual’s behavior is suspicious. Security systems can then issue alerts to personnel, allowing them to intervene before a breach happens.
AI-powered analytics can help in monitoring large-scale events such as concerts, sports games, and public gatherings, identifying crowd surges or potential stampedes in real-time. This proactive approach allows security teams to take action before incidents escalate into critical situations.
AI in Access Control Systems
 AI is also reshaping access control by introducing biometric authentication, intelligent access policies, and adaptive security responses. Facial recognition, fingerprint scanning, and iris detection—powered by AI—are replacing traditional keycards and passwords, offering a more secure and frictionless experience for employees and visitors.
AI is also reshaping access control by introducing biometric authentication, intelligent access policies, and adaptive security responses. Facial recognition, fingerprint scanning, and iris detection—powered by AI—are replacing traditional keycards and passwords, offering a more secure and frictionless experience for employees and visitors.
AI-driven access control systems can adapt to evolving security threats by learning user behaviors and flagging anomalies. If an employee suddenly tries to access a restricted area at an unusual time, the system can trigger additional authentication steps or alert security personnel. These AI-powered systems can also integrate with databases to enforce blacklists and whitelist protocols, enhancing perimeter security.
Additionally, AI-enhanced access control can be used in conjunction with workforce management, allowing for more efficient tracking of employee attendance, automated credential revocation for terminated employees, and secure remote access for approved personnel.
AI-Driven Robotics and Drones
The deployment of AI-powered security robots and drones is becoming more common in large-scale facilities, such as airports, warehouses, and corporate campuses. These autonomous systems can patrol designated areas, analyze footage in real-time, and even interact with potential threats using voice commands or alerts.
Security robots equipped with AI can identify suspicious behavior, recognize unauthorized personnel, and conduct temperature scans in high-risk areas. AI-driven drones, on the other hand, provide aerial surveillance, offering a broader perspective of security perimeters, which is particularly useful for securing large or remote locations where manual patrols are less effective.
Furthermore, these AI-powered security agents can work around the clock, reducing the need for human patrols while maintaining a consistent level of monitoring. Some of the latest models are equipped with environmental sensors that detect hazardous materials, making them valuable assets for critical infrastructure protection.
AI and Cybersecurity Convergence
As physical security systems become more connected, the risk of cyber threats increases. AI is playing a crucial role in bridging the gap between physical and cybersecurity by identifying vulnerabilities and mitigating risks in real time. AI-driven security platforms use behavior-based analytics to detect unauthorized access to surveillance networks, monitor unusual login attempts, and prevent data breaches.
AI-enhanced threat detection software can scan large amounts of data to recognize malware, ransomware, and phishing attempts, protecting security infrastructures from cyberattacks. By integrating AI with both cybersecurity and physical security systems, organizations can establish a more holistic security approach that safeguards against both digital and physical threats.
Security Information and Event Management (SIEM) platforms and Security Orchestration, Automation, and Response (SOAR) solutions are increasingly using AI to correlate events across different security layers. This ensures a more comprehensive security posture by automatically identifying, prioritizing, and responding to both cyber and physical security incidents in real time.
Future Outlook: The Growth of AI in Security
The integration of AI into the physical security industry is only expected to grow. Market analysts predict that investments in AI-driven security solutions will continue to rise as businesses, government agencies, and critical infrastructure providers seek more efficient ways to protect assets and people.
As AI technology evolves, new applications such as real-time audio threat detection, emotion recognition, and AI-enhanced forensic analysis will become more common. AI will also play a key role in autonomous security decision-making, reducing the reliance on human intervention and improving response times in emergency situations.
Future advancements in AI will also lead to more sophisticated autonomous security solutions, including AI-powered facial recognition gates for seamless access control, smart city surveillance integrations, and advanced threat prediction models that adapt in real time.
AI is Reshaping Physical Security
AI is reshaping the physical security landscape by providing smarter, faster, and more accurate security solutions. From advanced video analytics to predictive threat detection, biometric authentication, and AI-driven robotics, the industry is embracing a new era of security innovation. Organizations investing in AI-powered security solutions are not only improving their defenses but also setting the foundation for a future where security is more proactive, adaptive, and intelligent than ever before. The rapid evolution of AI in security is setting the stage for a safer world, where threats are detected before they occur, and response times are reduced to a matter of seconds.
Please give us a call to explore the ways AI can help your physical security systems, policies and procedures.
 Although cloud-based systems are getting more popular, many security systems still have on-premise servers at their heart. Servers, like all electronics, can fail and will need to be replaced. Servers also need updating in many ways. Sometimes they can show signs of issues overnight, and sometimes more slowly over time. The overnight issues are easier to detect, but the slower failures can be harder to detect, so I thought I would share some things to look out for.
Although cloud-based systems are getting more popular, many security systems still have on-premise servers at their heart. Servers, like all electronics, can fail and will need to be replaced. Servers also need updating in many ways. Sometimes they can show signs of issues overnight, and sometimes more slowly over time. The overnight issues are easier to detect, but the slower failures can be harder to detect, so I thought I would share some things to look out for. Server software, like all software, can have security or feature updates. Server software like Windows, Linux, MAC OS, etc., needs to be maintained to have the latest features and security patches. Depending on the settings, security patches will download and install themselves, but if you’re not sure, you should check with your IT team.
Server software, like all software, can have security or feature updates. Server software like Windows, Linux, MAC OS, etc., needs to be maintained to have the latest features and security patches. Depending on the settings, security patches will download and install themselves, but if you’re not sure, you should check with your IT team.
 For those of you using Genetec™ access control systems… did you know that Genetec offers Federation™? Federated licensing in Genetec’s security solutions provides organizations with a flexible, efficient, and scalable way to manage and optimize their security licenses across multiple locations or systems, ultimately improving resource allocation and reducing operational costs.
For those of you using Genetec™ access control systems… did you know that Genetec offers Federation™? Federated licensing in Genetec’s security solutions provides organizations with a flexible, efficient, and scalable way to manage and optimize their security licenses across multiple locations or systems, ultimately improving resource allocation and reducing operational costs.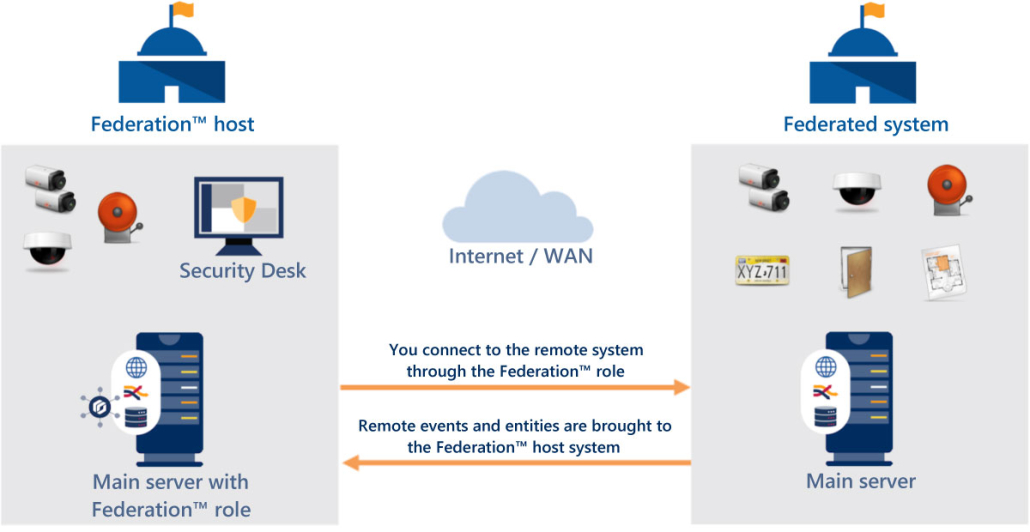
 In our continuing series of educational posts, we love sharing the layered capabilities of access control systems.
In our continuing series of educational posts, we love sharing the layered capabilities of access control systems. Randomized Control Experiments are considered to be one of the most effective ways to study cause-and-effect relationships. This method helps minimize biases by randomly assigning participants to either a treatment group (which receives the intervention) or a control group (which does not), ensuring that any differences between the groups can be attributed to the intervention itself, rather than other variables. This method is the gold standard in several major industries like medical intervention, psychology and more.
Randomized Control Experiments are considered to be one of the most effective ways to study cause-and-effect relationships. This method helps minimize biases by randomly assigning participants to either a treatment group (which receives the intervention) or a control group (which does not), ensuring that any differences between the groups can be attributed to the intervention itself, rather than other variables. This method is the gold standard in several major industries like medical intervention, psychology and more. At Kenton Brothers Systems for Security, we are always focused on Innovation. We have a great saying: Innovate or Die
At Kenton Brothers Systems for Security, we are always focused on Innovation. We have a great saying: Innovate or Die AI is also reshaping access control by introducing biometric authentication, intelligent access policies, and adaptive security responses. Facial recognition, fingerprint scanning, and iris detection—powered by AI—are replacing traditional keycards and passwords, offering a more secure and frictionless experience for employees and visitors.
AI is also reshaping access control by introducing biometric authentication, intelligent access policies, and adaptive security responses. Facial recognition, fingerprint scanning, and iris detection—powered by AI—are replacing traditional keycards and passwords, offering a more secure and frictionless experience for employees and visitors.