By David Strickland, Vice President of Kenton Brothers
Kenton Brothers is celebrating 125 years in business this year, and over those decades we’ve seen our share of innovative technology. KB was around for the first cars, motorized bikes, airplanes, rockets, robots and now security drones. As you may have read before, we believe strongly in the premise “Innovate or die”.
We get excited when technology innovates to solve a problem.
 Critical infrastructure protection has become a paramount concern for the US government and private organizations alike. From power plants to transportation hubs, food manufacturing to water and waste facilities… these sites are critical to a properly functioning society. Their importance makes them a prime target for a range of threats, from physical attacks to cyber-attacks. As far as commercial security goes, technology is playing a crucial role, and one such technological marvel is the drone.
Critical infrastructure protection has become a paramount concern for the US government and private organizations alike. From power plants to transportation hubs, food manufacturing to water and waste facilities… these sites are critical to a properly functioning society. Their importance makes them a prime target for a range of threats, from physical attacks to cyber-attacks. As far as commercial security goes, technology is playing a crucial role, and one such technological marvel is the drone.
Drones, once confined to hobbyists and aerial photography enthusiasts, have now emerged as powerful tools in the realm of physical security for critical infrastructure.
Terrorist organizations, criminal syndicates, and even disgruntled individuals may attempt to breach the security of critical infrastructure through physical means. These attacks can range from sabotage to theft of sensitive materials. To address these threats, security measures must be proactive, adaptable, and capable of providing real-time information. This is where drones come into play.
Guardian Angel – Aerial Surveillance
Drones offer a versatile platform for aerial surveillance. Equipped with high-definition cameras, thermal imaging, LIDAR and other advanced sensors, drones can provide a bird’s-eye view of critical infrastructure, offering security personnel unprecedented situational awareness. They can patrol vast areas efficiently and discreetly, making them ideal for spotting suspicious activities, unauthorized access, or potential vulnerabilities.
Incorporating machine learning algorithms and artificial intelligence, drones can be programmed to identify unusual behavior patterns, such as trespassing or loitering, and issue alerts in real-time. This proactive approach allows security teams to respond swiftly to potential threats before they escalate into security breaches. Unmanned aerial vehicles (UAVs) provide a rapid response and fast “eyes on” to the target area. They also provide live updates to control stations while active waypoint tracking can be maintained based on target parameters like thermal signatures.
A key advantage of a UAV is its ability to collect video.
 The video imagery captured by a UAV is ideally suited for reconnaissance or rapid situation awareness. It has the advantage for security personnel to detect and monitor potential threats from a safe distance. UAVs in perimeter security reduce the requirement for foot patrols by security guards. They provide real time situational awareness with the added perk of recording video for analysis later on.
The video imagery captured by a UAV is ideally suited for reconnaissance or rapid situation awareness. It has the advantage for security personnel to detect and monitor potential threats from a safe distance. UAVs in perimeter security reduce the requirement for foot patrols by security guards. They provide real time situational awareness with the added perk of recording video for analysis later on.
The speed, size, maneuverability, and additional technologies make UAVs the perfect supplement to ground security. They allow security teams to perform monitoring tasks more quickly and efficiently. For this reason, drones have a competitive edge over stationary cameras, as the drone can be flown at different times and be guided to blind spots.
Another significant advantage of using drones for commercial security is their ability to provide rapid intelligence and response. In the event of an intrusion or emergency, drones can be deployed within minutes, whereas traditional security personnel may take much longer to arrive at the scene. This quick response time can be critical in preventing or minimizing damage to critical infrastructure. Additionally, upon alert a drone can cover up to 10 times the area of a vehicle response in a fraction of the time.
Drones can also access areas that may be challenging or dangerous for human responders. Scenarious include climbing steep terrain or inspecting hard-to-reach locations like the tops of tall structures. This ensures that security teams have eyes on the situation even in the most challenging circumstances.
Super Human Capabilities
Drones equipped with environmental sensors can play a vital role in safeguarding critical infrastructure from natural disasters.
By regularly monitoring factors like water levels, temperature, humidity, and seismic activity, drones can provide early warnings and data for disaster preparedness and response plans.
For instance, a drone surveying a dam can detect signs of structural weakness or unusual water flow patterns, allowing for timely maintenance or intervention to prevent a catastrophic failure.
Similarly, drones can monitor forests surrounding power lines for signs of wildfires, helping utilities take proactive measures to prevent electrical equipment from sparking fires during dry, windy conditions.
Routine inspections of critical infrastructure are essential to ensure their continued operation and safety. Traditionally, these inspections have been carried out by human inspectors, often requiring extensive downtime and posing safety risks. Drones can revolutionize this process. Equipped with high-resolution cameras, infrared sensors and low frequency radar, drones can conduct detailed inspections of infrastructure such as bridges, pipelines, and power lines. They can capture images and data that are difficult or impossible for human inspectors to obtain.
As critical infrastructure continues to be a prime target for a wide range of threats, the adoption of drone technology for physical security is becoming increasingly important.
Drones offer a unique set of capabilities, including aerial surveillance, rapid response, environmental monitoring, infrastructure inspection, and scalability. Like we mentioned, our team at Kenton Brothers Systems for Security gets excited when technology innovates to solve a problem. In this case, drones and critical infrastructure are a match made in heaven and we couldn’t be more excited!
If you are thinking about ways to help secure your critical infrastructure location and would like to explore the use of drones, please let us know and we will set up a demo with you!



 We recently received a Chain of Custody request from one of our banking clients. They had an event that they deemed legally significant and requested our help in documenting what had happened. They needed our help to get the video segments exported properly. They wanted footage from all of the cameras at one of their locations over the past 30 days. (That’s a good amount of video data!)
We recently received a Chain of Custody request from one of our banking clients. They had an event that they deemed legally significant and requested our help in documenting what had happened. They needed our help to get the video segments exported properly. They wanted footage from all of the cameras at one of their locations over the past 30 days. (That’s a good amount of video data!) Chain of Custody is something Kenton Brothers takes extremely seriously for many reasons. One, we want to make sure we are providing our customers with a level of service and reliability they can count on. We also want to make sure law enforcement has what they need to support or refute claims. This is also a great example of how the commercial security systems we sell and support do what they’re supposed to do.
Chain of Custody is something Kenton Brothers takes extremely seriously for many reasons. One, we want to make sure we are providing our customers with a level of service and reliability they can count on. We also want to make sure law enforcement has what they need to support or refute claims. This is also a great example of how the commercial security systems we sell and support do what they’re supposed to do. Critical infrastructure protection has become a paramount concern for the US government and private organizations alike. From power plants to transportation hubs, food manufacturing to water and waste facilities… these sites are critical to a properly functioning society. Their importance makes them a prime target for a range of threats, from physical attacks to cyber-attacks. As far as commercial security goes, technology is playing a crucial role, and one such technological marvel is the drone.
Critical infrastructure protection has become a paramount concern for the US government and private organizations alike. From power plants to transportation hubs, food manufacturing to water and waste facilities… these sites are critical to a properly functioning society. Their importance makes them a prime target for a range of threats, from physical attacks to cyber-attacks. As far as commercial security goes, technology is playing a crucial role, and one such technological marvel is the drone. The video imagery captured by a UAV is ideally suited for reconnaissance or rapid situation awareness. It has the advantage for security personnel to detect and monitor potential threats from a safe distance. UAVs in perimeter security reduce the requirement for foot patrols by security guards. They provide real time situational awareness with the added perk of recording video for analysis later on.
The video imagery captured by a UAV is ideally suited for reconnaissance or rapid situation awareness. It has the advantage for security personnel to detect and monitor potential threats from a safe distance. UAVs in perimeter security reduce the requirement for foot patrols by security guards. They provide real time situational awareness with the added perk of recording video for analysis later on. As in all security, it only takes one weak link to bring the whole castle down. You can have the best moat, the best turrets, and the best drawbridge. But if there was a secret, unguarded passage and the enemy discovered it, it could certainly lead to your demise. In the commercial access control world, the Weigand Protocol is that un-guarded secret passage.
As in all security, it only takes one weak link to bring the whole castle down. You can have the best moat, the best turrets, and the best drawbridge. But if there was a secret, unguarded passage and the enemy discovered it, it could certainly lead to your demise. In the commercial access control world, the Weigand Protocol is that un-guarded secret passage.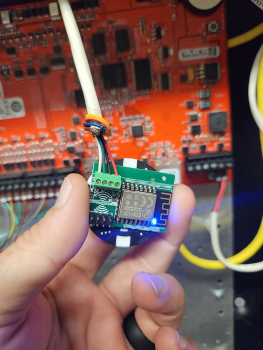 If you look online, you can find a board that can be installed between a reader and control panel that will intercept and log every access card being used. The board is smaller than a poker chip and can be installed behind a reader pretty easily. Once installed, it is powered by the door controller and is completely invisible to the reader and access control system. The attacker can leave it in place for a few days or a few weeks, while it collects every card read. Then, when they are ready, they can retrieve the list of cards from the built-in Wi-Fi interface. If the attacker only needs access to get into that single door, they can even “replay” the card number from the Weigand interface back to the door controller, probably granting access. If they need access to multiple doors, they could use the information to recreate identical cards to the ones you are using.
If you look online, you can find a board that can be installed between a reader and control panel that will intercept and log every access card being used. The board is smaller than a poker chip and can be installed behind a reader pretty easily. Once installed, it is powered by the door controller and is completely invisible to the reader and access control system. The attacker can leave it in place for a few days or a few weeks, while it collects every card read. Then, when they are ready, they can retrieve the list of cards from the built-in Wi-Fi interface. If the attacker only needs access to get into that single door, they can even “replay” the card number from the Weigand interface back to the door controller, probably granting access. If they need access to multiple doors, they could use the information to recreate identical cards to the ones you are using. I need to mention a side note here for
I need to mention a side note here for  When walking through Kenton Brothers Systems for Security, you will see this phrase prominently displayed on the walls throughout our building. Innovation is one of our core values and it’s a big reason we continue to provide remarkable physical security solutions for our customers… going on 126 years.
When walking through Kenton Brothers Systems for Security, you will see this phrase prominently displayed on the walls throughout our building. Innovation is one of our core values and it’s a big reason we continue to provide remarkable physical security solutions for our customers… going on 126 years. Facial recognition technology operates at impressive speeds, providing real-time identification results. This capability is especially valuable in high-traffic areas like airports, offices, and educational institutions, where quick and efficient access control is necessary. The system can process multiple faces simultaneously, reducing bottlenecks and ensuring smooth entry flows.
Facial recognition technology operates at impressive speeds, providing real-time identification results. This capability is especially valuable in high-traffic areas like airports, offices, and educational institutions, where quick and efficient access control is necessary. The system can process multiple faces simultaneously, reducing bottlenecks and ensuring smooth entry flows.