Top 10 tips for raising the cybersecurity bar in your organization today!
By David Strickland, Vice President of Kenton Brothers
 October is Cybersecurity awareness month!
October is Cybersecurity awareness month!
CISA, or the Cybersecurity and Infrastructure Security Agency, celebrates October as the month to get in the know.
Kenton Brothers Systems for Security would like to remind you that many of your physical security systems run on an IP (Internet Protocol) network. These include IP video surveillance and IP based access control systems. In an effort to help support our customers and bring about greater awareness of the risks surrounding Cybersecurity, we thought it would be good to create a guide for some of the best practices around cybersecurity for your organization.
Here are 10 ways to raise the cybersecurity bar in your organization today!
1) PASSWORD PROTECT EVERY DEVICE
Every device that connects to the internet in any way should have a password. It should not be the default password from the manufacturer. A strong password is at least 12 characters that are a mix of numbers, symbols, and capital lowercase letters. Never reuse passwords and don’t share them on the phone, in texts, or by email. Limit the number of unsuccessful log-in attempts to limit brute force password-guessing attacks. Configure your systems to require passwords be changed at least quarterly.
2) UPDATE YOUR OPERATING SYSTEM AND DEVICE FIRMWARE
This includes your apps, web browsers, and operating systems. It may also include your software upgrades for security devices such as cameras and access control controllers. If possible, set updates to happen automatically. Many of these updates include patches and fixes for vulnerabilities that have been discovered.
 3) USE MULTI-FACTOR AUTHENTICATION
3) USE MULTI-FACTOR AUTHENTICATION
Require multi-factor authentication to access areas of your network containing sensitive information. This requires additional steps beyond logging in with a password — like a temporary code on a smartphone or a key that’s inserted into a computer.
4) ENCRYPT YOUR DEVICES
Encrypt devices and other media that contain sensitive personal information. These include laptops, tablets, smartphones, removable drives, backup tapes, and cloud storage solutions.
5) DISABLE ALL PORTS NOT IN USE
Confirm that the organization’s IT personnel have disabled all ports and protocols that are not essential for business purposes. Switches that have open ports that have not been turned off are literally open doors to your data.
6) USE EMAIL AUTHENTICATION
When you set up your business email, make sure the email provider offers email authentication technology. That way, when you send an email from your company’s server, the receiving servers can confirm that the email is really from you. If it’s not, the receiving servers may block the email and foil an email imposter.
7) TRAIN YOUR STAFF
Teach your staff how to avoid phishing scams and show them some of the common ways computers and devices become infected. Include tips for spotting and protecting against Ransomware in your regular orientation and training. Also, train them to never share passwords or leave devices such as cell phones unattended or computers unlocked when they step away.

8) THINK BEFORE YOU CLICK
More than 90% of successful cyber-attacks start with a phishing email.
A phishing scheme is when a link or webpage looks legitimate, but it’s a trick designed by bad actors to have you reveal your passwords, social security number, credit card numbers, or other sensitive information. Once they have that information, they can use it on legitimate sites. And they may try to get you to run malicious software, also known as malware. If it’s a link you don’t recognize, trust your instincts, and think before you click.
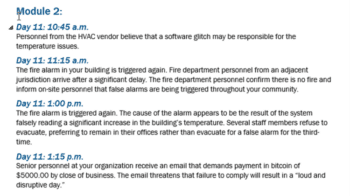
9) LOWER REPORTING THRESHOLDS:
Every organization should have documented thresholds for reporting potential cyber incidents to senior management and to the U.S. government. Senior management should establish an expectation that any indications of malicious cyber activity, even if blocked by security controls, should be reported to report@cisa.gov. Lowering thresholds will ensure we are able to immediately identify an issue and help protect against further attack or victims.
10) INSPECT, INSPECT, INSPECT!
You can have the greatest policies and procedures in the world. However, to get the best results you must test and inspect your system regularly. A member of senior leadership should randomly test and inspect your systems for compliance.
Need Some help implementing these standards? Give us a call!

 Hacking, at its root level, is a person using a computer program for a purpose that is not intended. It’s like discovering a person walking a dog and then using the dog to attack someone. That wasn’t the intent of the person walking the dog, but the hacker was able to take control. In order to “hack”, the attacker must find a weakness in the software and then exploit the weakness. In the ever-evolving game of cat and mouse, weaknesses get found and software gets modified to patch those weaknesses.
Hacking, at its root level, is a person using a computer program for a purpose that is not intended. It’s like discovering a person walking a dog and then using the dog to attack someone. That wasn’t the intent of the person walking the dog, but the hacker was able to take control. In order to “hack”, the attacker must find a weakness in the software and then exploit the weakness. In the ever-evolving game of cat and mouse, weaknesses get found and software gets modified to patch those weaknesses.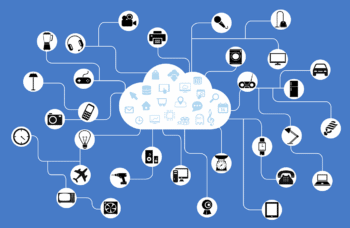 The Internet of Things (IoT) is defined as “a system of interrelated computing devices, mechanical and digital machines, objects, animals or people that are provided with unique identifiers (UIDs) and the ability to transfer data over a network without requiring human-to-human or human-to-computer interaction.”
The Internet of Things (IoT) is defined as “a system of interrelated computing devices, mechanical and digital machines, objects, animals or people that are provided with unique identifiers (UIDs) and the ability to transfer data over a network without requiring human-to-human or human-to-computer interaction.”